![[FA] SIT One SITizen Alumni Initiative_Web banner_1244px x 688px.jpg](/sites/default/files/2024-12/%5BFA%5D%20%20SIT%20One%20SITizen%20Alumni%20Initiative_Web%20banner_1244px%20x%20688px.jpg)
Programme Overview
The Bachelor of Engineering with Honours in Information and Communications Technology majoring in Information Security is a four-year direct honours degree programme; the first undergraduate degree programme offered by a local autonomous university that majors in information security.
The programme is designed to provide students with the necessary industry-relevant knowledge and practical technical skills to become specialised professionals in the field of information security that will be in demand by the industry.
Building on the core computer science fundamentals, specialised in-depth knowledge and technical skills will be taught to cover a holistic range of topics in Information Security. Students will learn about Secured Software Development, Ethical Hacking, Digital Forensics, Network Security, Web Security as well as Security Governance and Management. Security in emerging areas such as mobile and cloud security will also be covered.
The Programme’s Mission Statement
To train highly specialised professionals that can integrate seamlessly and contribute effectively to the Infocomm industry.
The Programme Educational Objectives
The programme aims to train students to become highly specialised professionals with deep technical capabilities that continuously improve themselves to be catalysts for transformation while remaining grounded in the community. As such, alumni of the programme are expected to achieve the following Programme Educational Objectives within five years after graduation:
- Demonstrate expertise in Software Engineering, Information Security or other specialised disciplines of ICT that is applicable in a broad range of industries.
- Solve complex interdisciplinary problems as part of a team leveraging on their individual deep technical competencies in ICT taking into consideration the requirements for the solutions to be sustainable and ethical.
- Demonstrate continuous professional and technical development through life-long learning such as obtaining advanced degrees, professional certifications, or knowledge of contemporary issues and recent advances to remain relevant in the dynamic field of ICT.
- Support the transformation of their profession and society through continuous engagements with their community.
Curriculum
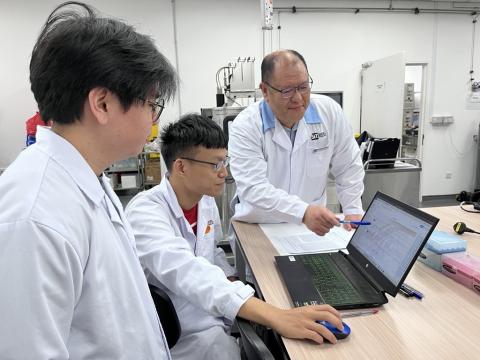
Team Integrated Project: During the course of the programme, students will be given the opportunity to develop innovative information security solutions with the industry through an Integrated Team Project.
Industry Certification Module: To further enhance their industry relevance, students will also be required to obtain at least one industry certification as part of the curriculum. This Industry Certification Module aims to promote life-long learning and inculcate students with the habit of keeping up with advances in technology even after graduation through industry certifications.
Integrated Work Study Programme (IWSP): To facilitate the seamless transition of graduates into the industry, a key feature of the curriculum is the IWSP. Students will embark on a year-long IWSP during their final year when they will take on real work and meaningful capstone projects with their host organisations.
To integrate the study component into their work experience, students will return to the university two mornings a week: one morning to consult their professors on their capstone project and to highlight their progress at work, and the other to attend flipped classes. During flipped classes, students will be able to bring their real work experience into the classroom for discussions. Ideas and solutions generated from these classroom discussions can then be brought back to their host organisations to promote innovation in the company.
After completing the degree programme, the students should satisfy the following Student Learning Outcomes (SLOs) as specified by the Engineering Accreditation Board (EAB):
Engineering Knowledge: Apply knowledge of mathematics, science, engineering fundamentals and an engineering specialization to the solution of complex engineering problems.
Problem Analysis: Identify, formulate, research literature and analyse complex engineering problems to reaching substantiated conclusions using first principles of mathematics, natural sciences and engineering sciences
Design/ Development of Solutions: Design solutions for complex engineering problems and design system components or processes that meet specified needs with appropriate consideration for public health and safety, cultural, societal and environmental considerations.
Investigation: Conduct investigations of complex problems using research-based knowledge and research methods including design of experiments, analysis and interpretation of data and synthesis of the information to provide valid conclusions.
Modern Tool Usage: Create, select and apply appropriate techniques, resources and modern engineering and IT tools including prediction and modelling to complex engineering activities with an understanding of the limitations.
The Engineer and the World: When solving complex engineering problems, analyse and evaluate sustainable development impacts to: society, the economy, sustainability, health and safety, legal frameworks and the environment
Ethics: Apply ethical principles and commit to professional ethics and responsibilities and norms of engineering practice.
Individual and Team Work: Function effectively as an individual, and as a member or leader in diverse teams and in multidisciplinary settings.
Communication: Communicate effectively on complex engineering activities with the engineering community and with society at large, such as being able to comprehend and write effective reports and design documentation, make effective presentations and give and receive clear instructions.
Project Management and Finance: Demonstrate knowledge and understanding of engineering and management principles and apply these to one’s own work, as a member and leader in a team, to manage projects and in multidisciplinary environments.
Life-long Learning: Recognize the need for and have the preparation and ability to engage in independent and life-long learning in the broadest context of technological change.
Accreditation
Accreditation of the programme will be sought with the EAB.
Career Opportunities
This programme will equip its graduates with the required academic knowledge and professional skill sets to take up specialist jobs in Information Security including, (and not limited to) Malware Analyst, Cyber Security Specialist, Information Security Systems Engineer, Pentester, Technical Information Security Officer, Application Security Analyst, IT Security Consultant, and IT Infrastructure Architect. Other than these specialist jobs, as the students are also well-grounded in generic computer science, they are not only employable in the field of Information Security but could also take on generic ICT job opportunities that are available to computer science graduates as well.
Integrated Work Study Programme
To facilitate the seamless transition of graduates into the industry, a key feature of the curriculum is the IWSP. Students will embark on a year-long IWSP during their final year when they will take on real work and meaningful capstone projects with their host organisations.
Overseas Immersion Programme
The Overseas Immersion Programme (OIP) is compulsory for all students pursuing SIT Undergraduate Programmes. In the second year, students will undergo a two-week Overseas Immersion Programme (module titled "Global Learning in ICT Advances") with our partner universities. These programmes are designed to provide a richer and more immersive global learning experience. Students will take part in lectures, hands-on project work, workshops, and industry visits as part of their overseas exposure.
Career Options
- Information Security Analyst/Professional
- Cyber Security Specialist
- Information Security Consultant
- Pen-tester
Programme Structure (AY2026/27)*
Programme Structure (AY2025/26)
| Module Title | Credits |
|---|---|
| Introduction to Computing | 6 |
| Programming Fundamentals | 6 |
| Computer Organization and Architecture | 6 |
| Mathematics 1 | 6 |
| Mathematics 2 | 6 |
| Operating Systems | 6 |
| Web Systems and Technologies | 6 |
| Object-Oriented Programming | 6 |
| Computer Networks | 6 |
| Ethics and Professional Conducts | 6 |
| Data Structures and Algorithms | 6 |
| Introduction to Software Engineering | 6 |
| Network Security | 6 |
| Ethical Hacking | 6 |
| Embedded Systems Programming | 6 |
| Applied Cryptography | 6 |
| Web Security | 6 |
| Mobile Security | 6 |
| Machine Learning | 6 |
| Global Learning in ICT Advances | 6 |
| Secure Software Development | 6 |
| Integrative Team Project | 6 |
| Operations Security and Incident Management | 6 |
| Malware Analysis and Defence | 6 |
| Security Analytics | 6 |
| Digital Forensics | 6 |
| Industry Certification Module | 6 |
| Special Topics in Security | 6 |
| Integrative Team Project 2 | 6 |
| Security Governance, Risk Management and Compliance | 6 |
| Integrated Work Study Programme | 30 |
| Capstone Project | 15 |
| Global Learning in ICT Advances | 6 |
* The programme structure is subject to change without prior notice. SIT regularly reviews its curriculum to ensure that it remains industry-relevant and prepares our students for the evolving needs of industry.
Eligibility and Exemption
Diploma holders from any of the five local polytechnics, A-Level / IB Diploma graduates, and holders of equivalent Year 12 qualifications are welcome to apply.
Holders of BCA Academy Diploma in Digital Engineering are eligible to apply.
Subject to approval, diploma holders may be granted exemptions for up to 10 modules based on modules taken during their diploma course. Exemptions may also be considered for relevant professional or industrial certifications.
Fees and Finances
Singapore Citizen
Permanent Resident
International Student
Industry Advisory Committee
The members of the Industry Advisory Committee for this programme are: