![[FA] SIT One SITizen Alumni Initiative_Web banner_1244px x 688px.jpg](/sites/default/files/2024-12/%5BFA%5D%20%20SIT%20One%20SITizen%20Alumni%20Initiative_Web%20banner_1244px%20x%20688px.jpg)
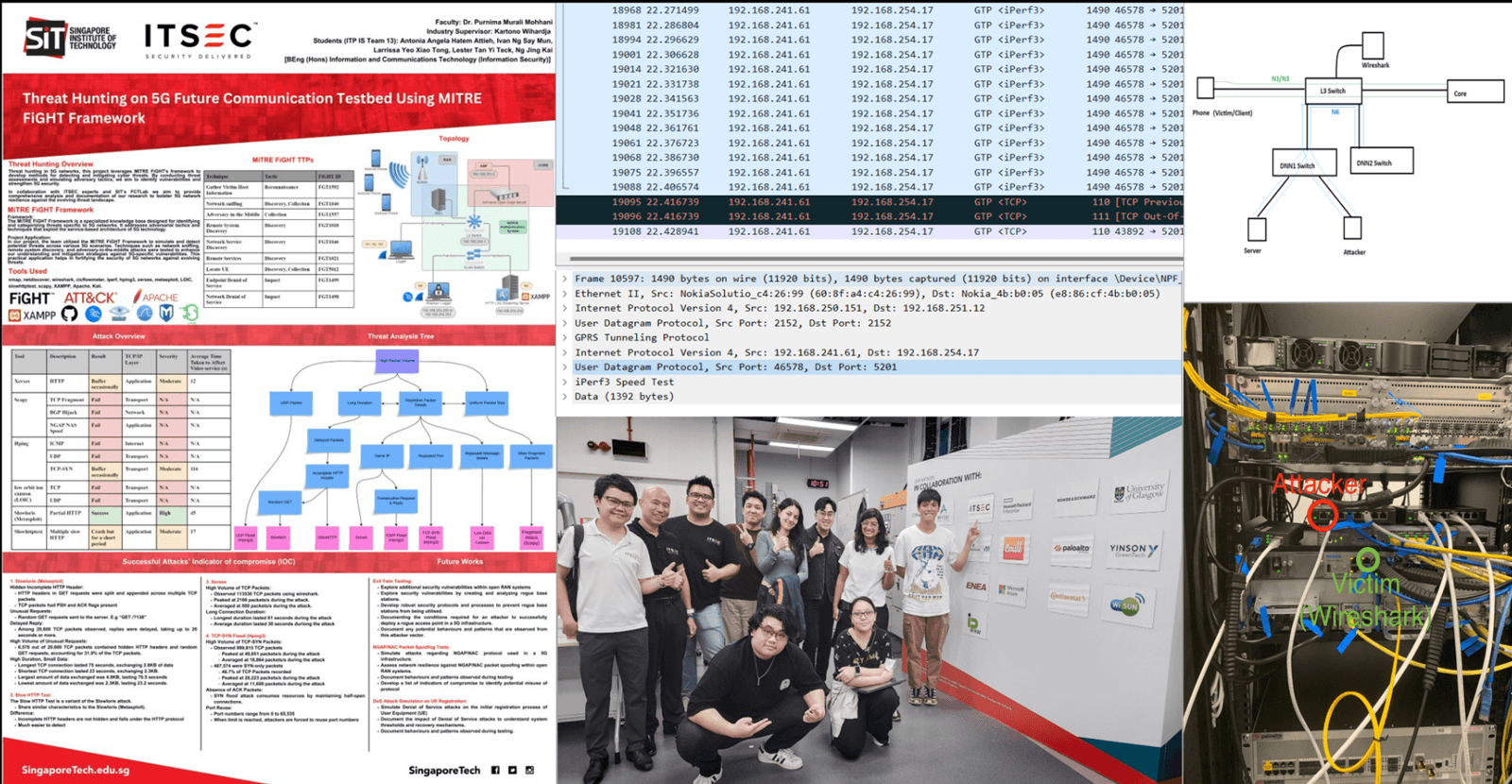
In collaboration with ITSEC Asia, this project explores 5G threat hunting scenarios aligned with the MITRE FiGHT framework, focusing on detecting Evil Twin attacks and other adversarial tactics across RAN, edge, and core
By leveraging private testbed environments, it supports the development of targeted, standards-driven defence strategies for next-gen telecom networks.
Project Deliverables/Outcomes/Impact:
- A. A. Hatem Attieh, L. Y. Xiao Tong, N. J. Kai, L. T. Yi Teck, I. N. Say Mun and P. M. Mohan, “Threat Hunting on5G Future Communication Testbed Using MITRE FiGHT Framework,” TENCON 2024 – 2024 IEEE Region 10Conference (TENCON), Singapore, Singapore, 2024, pp. 1-5, doi: 10.1109/TENCON61640.2024.10903058.
- “Validating Evil Twin Attacks in 5G/6G Based on the MITRE FiGHT” – Presented at the 2025 IEEE INFOCOM in May 2025